Create a New Educational Landscape with Devolity
Transforming The Educational Sector With Devolity Cutting-Edge It Solutions
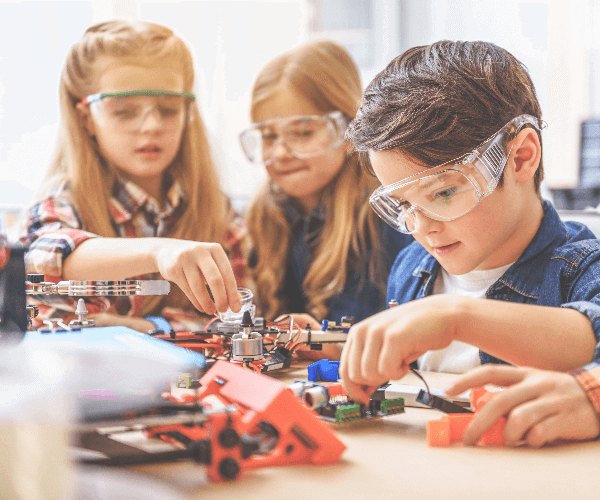
A well-balanced application of technology can improve any sector of society, the educational sector is no exception to this rule. There is always a need in the field of education for fresh approaches. So much has changed in this field during the previous few decades. One of the key players in this digital transformation is the IT solutions for the education sector.
Books aren't the only way to learn anymore. There is a progressive shift away from print and toward digital apps and websites. In addition, today's educators and learners alike value convenience and mobility, so they're on the lookout for individualized services they can access from anywhere using any device.
The tech specialists at Devolity offer a wide variety of e-learning solutions with the help of the cloud, AI, AR, VR, mobility, etc. They can do the assignment without a hitch and develop novel approaches to the problem. The variety of Devolity e-learning solutions are.
- Web Portal
- Learning Apps
- Virtual Classrooms
- Remote Learning Website
- Online Exam Portal
- Institute Administration Software
Improve the Educational Ecology with Devolity IT Solutions
Use Our Innovative Tools and Technologies to Unlock The Full Potential of Online Education

Intelligent IT Analytics
IT departments can't make good decisions unless they have access to data sets covering many areas of IT and can draw significant correlations from massive amounts of data. With the help of Devolity cutting-edge self-service analytics solutions, you may quickly and easily make informed IT decisions.

Mobile Learning Applications
Devolity mobile learning applications are responsive and adaptive, and they offer a variety of capabilities such as speech recognition, overwriting, self-evaluation, and m-books so that users may learn whenever, wherever, and however, they prefer.

E-Learning Solutions
Devolity professionals use cutting-edge data, trends, and tools to generate custom strategies, solutions, storyboards, and content for various industries.

Institute Management Solutions
Our outstanding institute management solutions help you to synchronize the institute's resources by streamlining and integrating its many different operations, processes, and information flows, among other things.

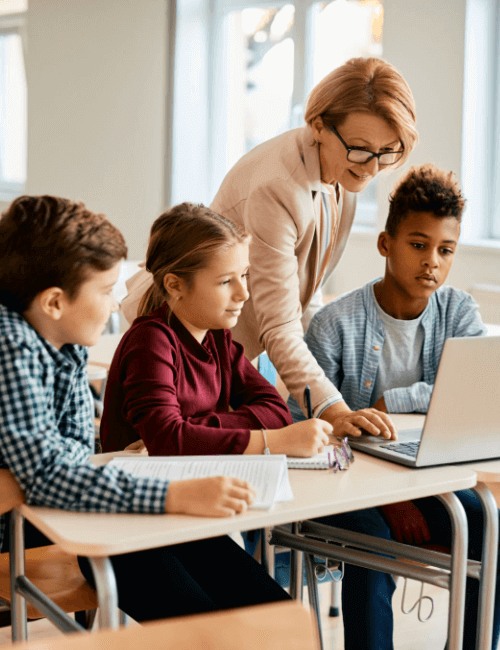
Virtual Classroom Solutions
Devolity offers in-depth subject expertise and provides enterprises with virtual classroom solutions that enable them to broadcast online lectures and tutorials at any time and from any location.
Advanced solutions for enhancing campus IT infrastructure
Devolity Provides a Unified Platform for the Administration of Academic Data for Both Students and Faculties
Devolity serves as a catalyst for educational institutions, helping them navigate and thrive in an ever-evolving landscape. We offer a comprehensive suite of education technology solutions tailored to address unique challenges, opportunities, and stakeholder expectations. Our services encompass strategy, architecture, development, and support, ensuring a holistic approach to your institution's needs. Additionally, we manage IT infrastructure and provide business process outsourcing to streamline operations and enhance efficiency.
- Institute Management Software
- Online Exam Portal
- E-Learning / LMS and Virtual Classroom
Discover The Reasons Behind Selecting Us.
Brands who trust on Devolity